DRPU USB Data Theft Protection Software
DRPU USB data theft protection tool monitors activities of USB mass storage devices configured on your PC. Software prevents data theft or block USB port access by unauthorized users of USB storage media in PC resulting in the prevention of data leakage.
Software provides facility to send log files of recorded data via E-mail option or upload log via FTP server. USB data theft protection software is capable to run in hidden mode and allow you to secretly record details of USB device plug in and plug out activities on your computer.
Software is suitable for all types of industries including small scale industries to large scale organization. Software provides an ultimate solution to restrict users from unauthorized access of important information, confidential files and folders, stored data, etc. through any type of USB drives on the computer.
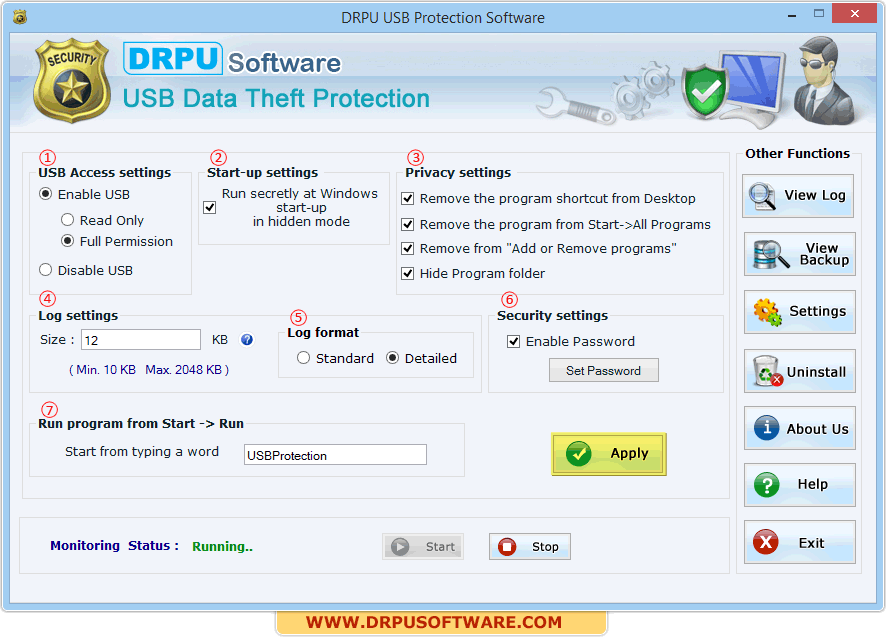
Above screenshot shows general settings including
USB Access setting – This option allows you to enable and disable USB access port.
Start-up settings – Select check box, if you want to run the software secretly at windows startup in hidden mode.
Privacy settings – Select check box, if you need to hide the program from desktop, start -> all program, “Add and remove program” and hide program folder.
Log settings – Use this option to set maximum size of text log and avoid over sizing of activities log.
Log Format – Enable either “Standard” or “Detailed” option to view recorded log file.
Security settings – Use this option to set password so that unauthorized user can not access the software settings.
Run program from Start -> Run – Enter any keyword in given space so that you can access the hidden software window by using run command (By default software window will be accessed by entering the default keyword “USBProtection” in run command).
Set all above options and then press “Apply” button to apply the software settings.
Supported USB Storage Devices:
Track activities of connection and removal of USB mass storage device.
USB protection tool block USB port access using USB access settings.
Provides facility to set password so that unauthorized user cannot access the software settings.
Option to view log file in HTML as well as Text file format.
Capability to capture photos of unauthorized user by enabling advance camera settings.
Facility to sent log file of recorded data and picture via Email and also have an option to upload the log and captures image on FTP server using FTP settings.
Secretly run and record USB storage media activities in hidden mode.
Save detail log of the USB drive activities performed by unknown user on your computer for future usage.
Facility to export and import all settings including general configuration settings, email settings and FTP settings if you want to install software in multiple machines.
User friendly graphical interface and smoothly run on all windows edition including windows 8/7/vista/XP and windows server 2000/2003/2008 etc.
Easy to install/uninstall software and no technical skill required to operate USB data theft protection tool.
Our Files & Database Converter Software :-